Implement cybersecurity in industrial environments
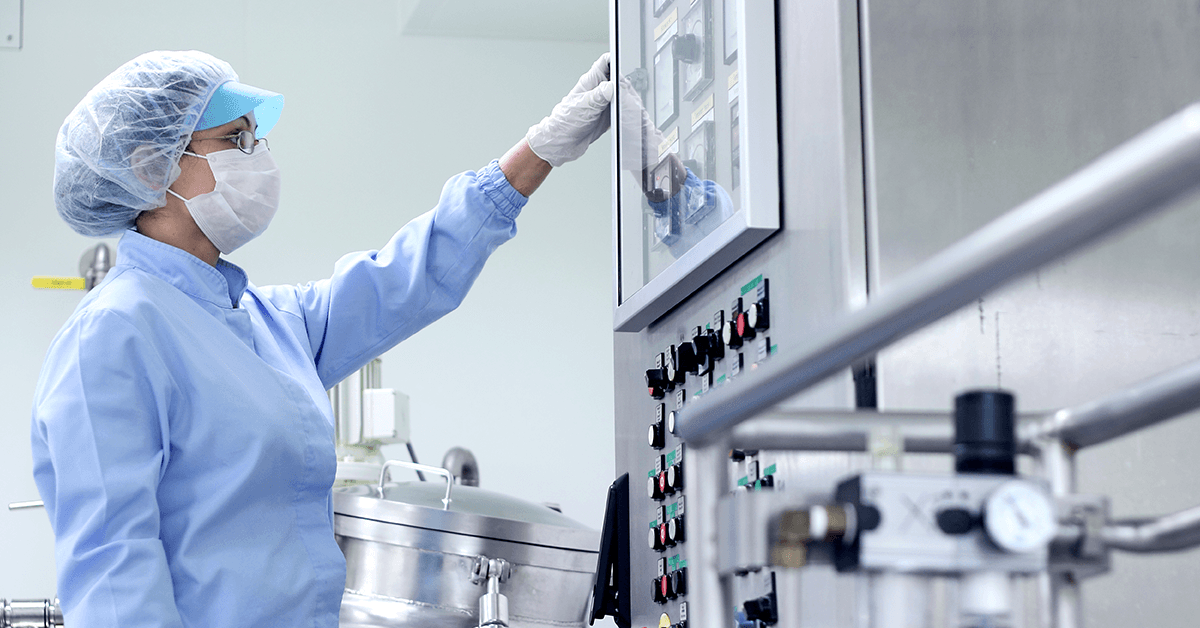
The rise of increasing security risks in industrial environments opens new security issues in the OT environments as well.
The process systems are a tempting target
By introducing new automation technologies to the industry and by digitalising processes, the “isolated” operating environments have become “open” and under threat against digitally targeted attacks.
The attackers exploit the vulnerabilities of legacy operating systems and devices, since security updates are not implemented regularly. This is why cybersecurity is critical in OT environments.
Vulnerable industrial environments





It is high time for industrial cybersecurity
Cyber security is introduced into the OT through measures and mechanisms that are already embedded into the basic process system development concepts. System anomalies, as well as successful cyber attacks, can make the system unavailable or cause it to restart or shut down completely.
Cyber security in OT: Business and technical advantages
The introduction of cybersecurity measures and mechanisms into the industrial environments brings:
✓ Improved surveillance and security systems
✓ Improved reliability and availability of systems
✓ Lower maintenance costs
✓ Increased investor confidence
✓ Improved reputation of the company
✓ Lower insurance premiums
✓ Stable and well organised work environment for the employees
Secure your industrial control system (ICS) environments
Protecting infrastructure against cyber threats is critical in any Operational Technology (OT) environment.
With Trend Micro ICS solutions you can ensure network segmentation and protect mission-critical devices from advanced cyberattacks.
Reduce security risks
Wondering which solution designed to build or enhance cybersecurity is right for you? Our cybersecurity experts can help you.
Our competency advantages
Our partners
We work with global leaders in specific technology segments.




















